Runtime Workload Monitoring #
Control ID: SDLC-CTRL-0016 | Type: Detective
Summary #
Production workloads are continuously monitored to detect and alert on any non-compliant or unauthorised changes in real time.
Mitigates Risk
SDLC-RISK-0001:
Supply Chain Compromise
SDLC-RISK-0002:
Insider Threat
SDLC-RISK-0003:
Unauthorised Deployment
SDLC-RISK-0005:
Vulnerable Software in Production
SDLC-RISK-0006:
Audit and Compliance Failure
SDLC-RISK-0009:
Environment Breach
Description #
Ensuring that risks are controlled in the value stream is the first level of software process compliance. Beyond this, it is important to have a monitoring process in place to ensure that unknown or non-compliant workloads are identified in production.
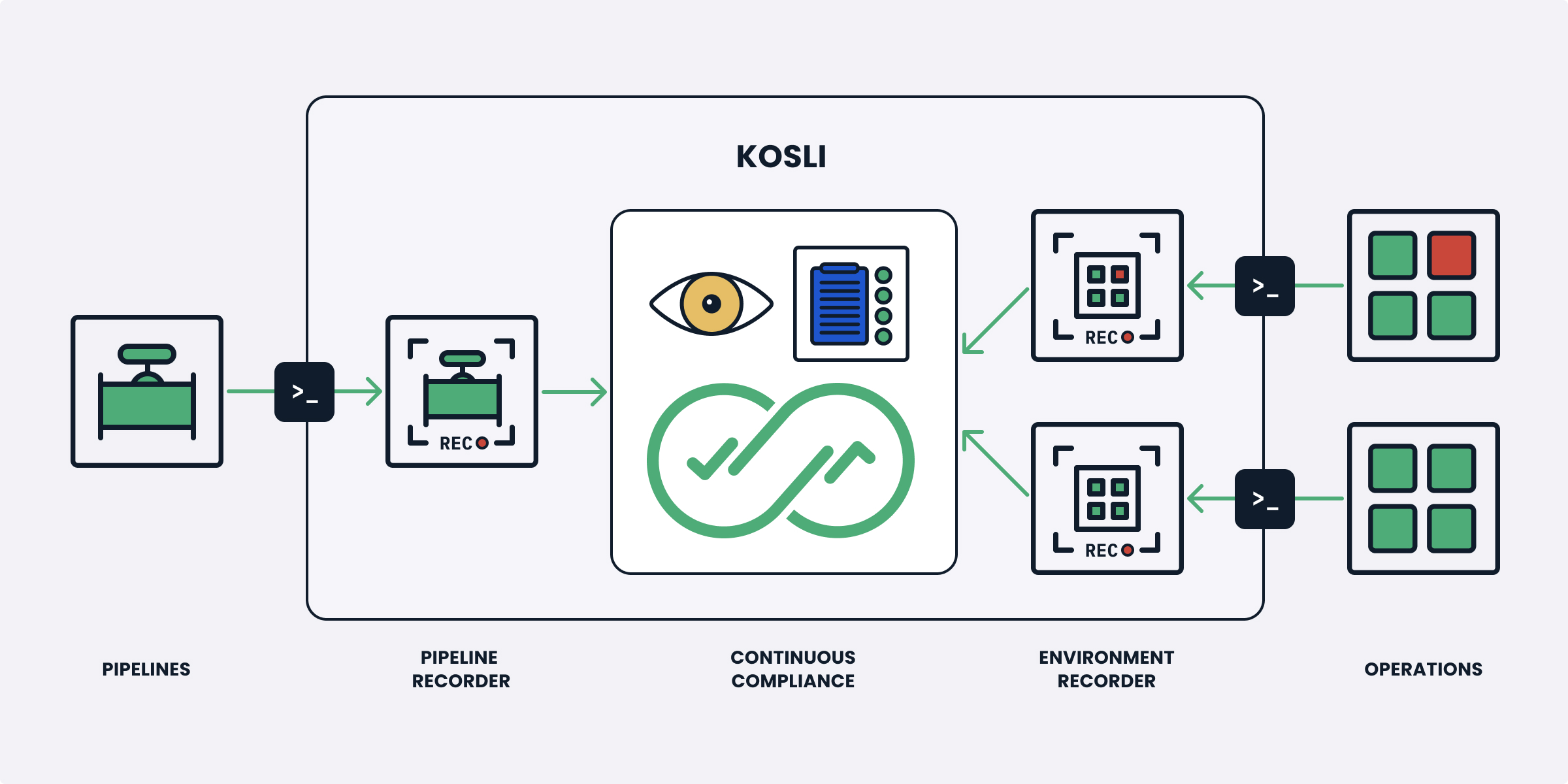
Runtime workload monitoring provides a forensic history of all changes to production environments, enabling retrospective analysis of what was running at any point in time. Combined with deployment controls, it creates a closed-loop compliance system that both prevents and detects unauthorised changes.
Requirements #
- All production workloads MUST be continuously monitored for compliance status
- Non-compliant or unauthorised workloads MUST generate alerts
- A forensic history of all workload changes MUST be maintained
- Monitoring MUST cover all runtime environments including containers, serverless functions, and storage
- Alert notifications MUST be delivered to the appropriate response channels
How we implement this control #
- A full forensic history of all container runtimes, lambda functions and S3 buckets are recorded using Kosli environments and can be found here: https://app.kosli.com/kosli/environments/
- Unauthorised or non-compliant workloads are recorded and create alerts in our Slack channels
Compliance Frameworks #
NIST SP 800-53 Rev. 5
- CA-7 — Continuous monitoring — runtime workload monitoring provides real-time compliance assurance across all environments.
- SI-4 — System monitoring — requires monitoring of production systems for unauthorised changes and anomalous behaviour.
- CM-8 — System component inventory — workload monitoring maintains a live inventory of all running components.
- IR-4 — Incident handling — non-compliant workload alerts feed directly into incident response processes.
- AU-6 — Audit record review — forensic history of workload changes supports ongoing analysis and reporting.
SOC 2 Type II
- CC7.2 — Requires monitoring of system components for anomalies; workload monitoring detects abnormal resource usage and service degradation.
- CC7.3 — Requires evaluation of security events; monitoring and alerting enable timely investigation and response to incidents.
- A1.2 — Requires environmental protections and monitoring of infrastructure; workload monitoring provides visibility into service availability and health.